Keeping track of USB assets and to whom they were assigned can be overwhelming. For years we relied on spreadsheets and trusted that folks would keep them current. Many companies and organizations have given up on keeping track of USB items such as keyboards, mice, and even monitors.
I have seen where the capital costs for tracking assets have continued to rise in an effort to unburden IT Asset Managers. Some companies may enforce a rule stating that they consider items costing less than $1,000 as disposable and do not require further tracking.
Unfortunately, some items still require oversight and accountability. These things can include printers and scanners that connect with USB, along with other items. Their software reveals weaknesses that hackers can exploit. BMC Client Management has a solution to mitigate the LOE (Level of Effort) to track these assets.
Use Case Examples:
- Medical organizations with over 30 physical offices where receptionists use their PCs to scan patients. This scanner digitizes the patient’s insurance card and government issues ID card and attaches them to the patient’s file. A lifecycle policy is in place where these devices must be replaced every four years, and all software must be removed from the old scanner and installed before attaching the scanner to the PC.
- HR departments are allowed to use USB-connected printers due to privacy concerns using a common network printer. To comply with HIPPA laws and for general auditing purposes, you must print any documents in a secured room or office.
- Web conferencing equipment as simple as a web camera (external) or sophisticated as the most expensive on the market needs to be tracked due to security policies and who has the right to use video outside of the organization (US Dept. of Defense as an example).
- Manufacturing that creates BAR CODE labels for packaging and shipping. We all love Zebra Printers!
How can BMC Client Management capture this data in real time?
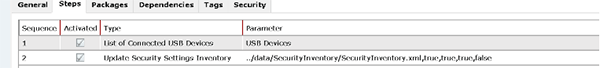
Once a device has an agent installed, an Operational Rule (our name for a script) can be assigned to that device or a group of devices to either run only once or on a repeated schedule that will keep track of USB asset-connected devices when the rule is executed. It will then update the application’s database so the IT Asset Manager can have complete visibility of what is plugged into that device or any device the script has run on.
To be current on all USB-connected devices, this rule should run on a regular schedule, such as “on computer startup” or “on user login.” Our method of collecting data is as minimal as possible. On the first run, we send in a “full” inventory. During subsequent executions, the application submits only the data that has changed from the last collection to the database.
How easy is it to capture this information?
Using a pre-configured Operational Rule Step (script) and selecting it from the available steps along with a second step to upload the data from the targeted device(s), this can be created, assigned, and reviewed from the collected data in less than a few minutes.
What data does the “Inventory” capture and add?
The main goal of this exercise is to ID all devices that have a Fujitsu USB Scanner.
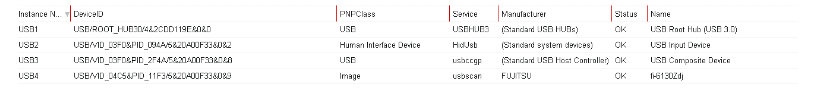
From the screenshot above, you can see the last item listed is indeed a scanner made by Fujitsu, and the model is a FUJITSU Image Scanner “fi-6130Z”. – Fujitsu Singapore.
How can we use this information?
After collecting the data, the next logical step is to create a query to isolate these objects from all the rest using the Client Management Query Builder. It is a simple-to-use tool where no prior SQL query language experience is required.
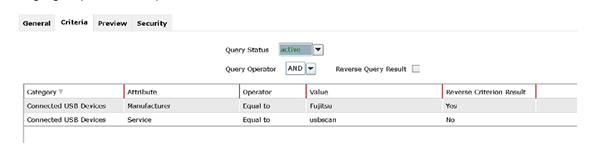
This query can be used to build a group of all the devices that are using this USB Scanner for further management and situational awareness. It can also be used to populate a report that can include specifics about the device the scanner is attached to, like location, primary user, IP address, OS version, etc.
Summary
Having the power of BMC Client Management at the disposal of the IT Asset Manager can significantly reduce the LOE required to track assets, replace aging assets, and ensure the software required to run this hardware is fully compliant with security standards for audit requirements.
