BMC Helix Remediate
Deploy in the cloud of your choice to strengthen security, improve productivity, and lower costs.
BMC Helix Remediate uses advanced analytics and automation to rapidly remediate security vulnerabilities for both on-premises and cloud-based infrastructure.
Automated security vulnerability management for 14x faster remediation
- Imports and analyzes data from vulnerability scanners, maps vulnerabilities to assets and patches, help set priorities, and automates corrective action
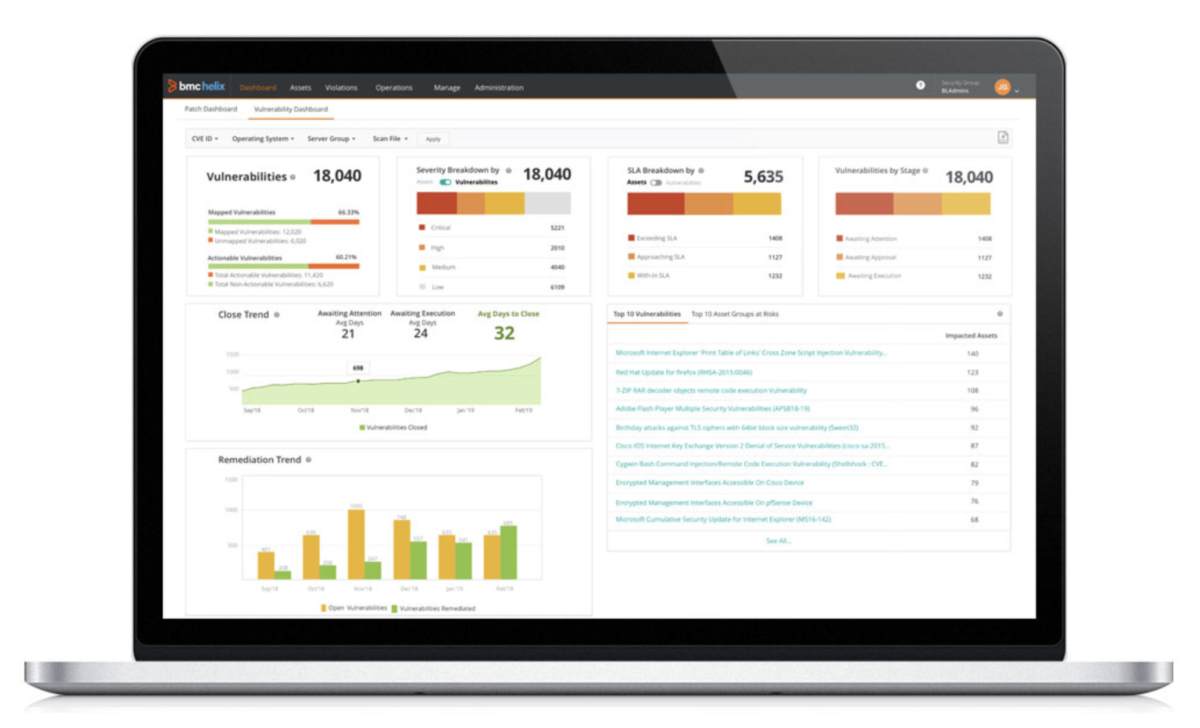
- Provides real-time visibility into security vulnerabilities, missing patches, and misconfigured resources
- Uses simplified patching for rapid remediation of security vulnerabilities both on-premises and in the cloud
- Automates configuration testing and remediation for resources on AWS, Azure, and GCP to ensure cloud services and containers are managed consistently and securely
- Provides container configuration security for Docker and Kubernetes
Reduce the risk of a breach by automating the collection, analysis, and remediation of security vulnerabilities
- Collect and analyze vulnerabilities in your hybrid cloud, remediate based on severity and impact to protect data, and keep business services up and running
- Remediate vulnerabilities with automated patch and configuration management to close more vulnerabilities in less time, raise productivity, lower costs, and increase efficiency
- Test and remediate configurations of cloud resources and containers to ensure compliance with custom policies as well as CIS, PCI, and GDPR
Automate and simplify patch management to boost productivity, increase efficiency, and quickly close security vulnerabilities
- Leverage state-of-the-art automation console designed for ease-of-use and simplification of patch deployments
- Create patch workflows with just a few clicks
- Reduce the number of patch deployment jobs required with policy-based patching
- Obtain visibility into vulnerabilities, severities, SLAs, trends, and remediation status using specialized patch dashboards
Manage configurations of cloud services and containers for greater security and consistency
- Use automation to check cloud resources, identify misconfigurations, and remediate
- Automate cloud configuration security posture management (CSPM) using Center for Internet Security (CIS) policies and your own custom policies
- Securely and consistently manage and remediate configurations of PaaS and IaaS services on your choice of cloud
- Improve container configuration security, including Kubernetes pods, hosts, Docker Daemon, image, and Docker container
- Begin improving your cloud configuration security in less than 5 minutes by taking advantage of the SaaS deployment model
Ready to take the next step?
Get in touch to get started
No obligation, no pressure.
We're easy to talk with and you might be surprised at how much you can learn about your project by speaking with our experts.
RightStar Headquarters
1801 Alexander Bell Dr
Ste 550
Reston, VA 20191-4344
(703) 242-7200
(703) 242-7599 Fax
